Internet inter-domain routing is controlled by commercial relationships among Autonomous Systems (ASes). As a consequence, although network connectivity may imply a large number of potential paths between source and destination domains, commercial relationships between ASes restrict the number of feasible paths that can be used to carry traffic from the source to the destination to a small set.
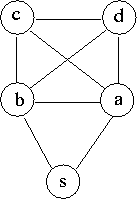
For instance, consider the network topology as shown in Fig. 1, which has 5 nodes. As shown in Fig.2(a), there are 10 topological routes (i.e., loop-free routes) implied by the network connectivity between source node s and destination d. In contrast, there are only 2 feasible routes from s to d that are supported by the AS relationships (Fig. 2(b)), assuming ASes a, b, c, and d peer with each other, and a and b are provider of AS s. Of more importance to packet filtering is the fact that, although network topology may imply all neighbors of a node can forward a packet allegedly from a source to the node, feasible routes constrained by routing policies help limit the set of such neighbors. As an example, let us consider the situation at node d. Given that only nodes a and b (but not c) are on the feasible routes from s to d as node d concerns, node d can infer that all packets forwarded by node c and allegedly from source s are spoofed and should be discarded.
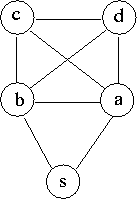
Fig. 1
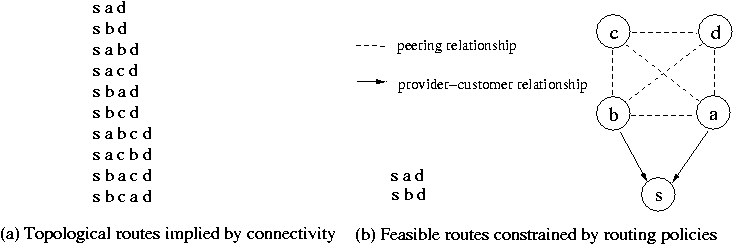
Fig. 2
IDPF is an inter-domain packet filter scheme based on the above observation. IDPFs can be deployed at border routers of an AS domain, they rely on locally exchanged BGP updates to infer the upstream neighbors on feasible routes from source to destination domains that can be used to carry traffic from the source to the destination. Through analysis, we show that IDPFs are correct in that they will not discard packets with valid source IP addresses, if all ASes on the Internet follow a set of route export policies, which are commonly used by today's ASes. Through simulation, we show that even with partial deployment on the Internet, IDPFs can proactively limit the spoofing capability of attackers. In addition, they can help localize the origin of an attack packet to a small number of candidate networks.
Zhenhai Duan, Xin Yuan, Jaideep Chandrashkar, "Constructing Inter-Domain Packet Filters to Control IP Spoofing Based on BGP Updates". In Proc. IEEE INFOCOM 2006. [PDF][Talk Slides]
Please download the original dpf simulator developed by Prof. Kihong Park's group at Purdue University, and then apply the following patch DPF.patch, which contains the changes we made to the dpf source code, a few cover selection and measurement programs.