The Internet
The Internet is the world-spanning collection of gear that speaks IPv4 or IPv6, and the networks that connect them.
In contrast to the halcyon days of yore (the 1980s) when all machines (all 10,000 of them) on the Internet were peers, nowadays we have a distinct hierarchy in place.
The Internet
At the bottom are the machines that you see everyday: mobile equipment, desktops, and all of the rest of the developing Internet of Things.
A layer above them are the Tier3 routers that entities like ISPs usually provide. Above the Tier3 routers most of the larger entities provide a Tier2 structure; finally, companies like Level3 provide Tier1 interconnectivity.
Wikipedia Creative Commons Illustration
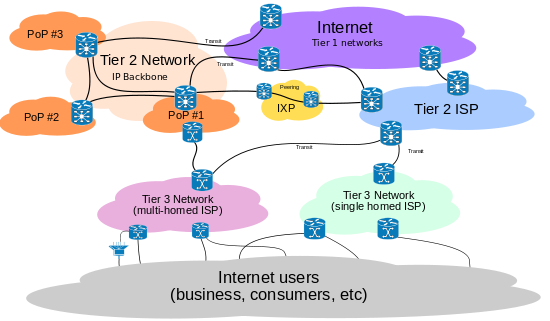
From http://en.wikipedia.org/wiki/File:Internet_Connectivity_Distribution_%26_Core.svg
Naming the Internet
Those familiar names that so many people associated with the Internet (www.facebook.com, www.google.com, www.reddit.com) are not actually "Internet" anything. The Internet is built over IP numbers, not these "names."
Instead the naming system is called "DNS" (Domain Naming System). It actually runs over port 53 (usually using UDP, though TCP is sometimes seen).
What happens is that when you ask to connect to, say, www.facebook.com, your browser has to find an IP number associated with that name.
Finding numbers for names
$ host www.facebook.com www.facebook.com is an alias for star.c10r.facebook.com. star.c10r.facebook.com has address 69.171.242.27 star.c10r.facebook.com has IPv6 address 2a03:2880:2030:2f01:face:b00c:0:8 star.c10r.facebook.com mail is handled by 10 smtpin.mx.facebook.com.
Here's an example of finding IP numbers for a DNS name using the "host" program.
$ echo -e "GET / HTTP/1.1\n\rHost: www.facebook.com\n\r" | nc 69.171.242.27 80 HTTP/1.1 302 Found Location: https://69.171.242.27/ Content-Type: text/html; charset=utf-8 X-FB-Debug: 4z6b6J3TQf9Z0br5bh/FkB+1Dtth3QeRxyKa6lcgmqo= Date: Tue, 02 Apr 2013 18:49:33 GMT Connection: keep-alive Content-Length: 0
Old versus new network tools
| Old | New |
| rlogin (never use) | ssh |
| telnet (shouldn't use) | ssh, nc |
| ftp (only for anonymous ftp) | sftp, ftp |
| rcp (never use) | scp |
| finger (shouldn't use) | NONE |
"Do"s and "Don't"s
The upshot of the previous page is that you should only use the programs ssh, sftp, scp, and nc for most network activities.
You should only use ftp for anonymous ftp, which is a pretty rare activity these days, though places like redhat.com still (sort of) support it.
Creating a SSH key
It's safer to not use a password for logging in. Instead use a private/public key pair.
Such a pair is easy to generate with ssh-keygen:
$ ssh-keygen Generating public/private rsa key pair. Enter file in which to save the key (/home/langley/.ssh/id_rsa): /tmp/testfile Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /tmp/testfile. Your public key has been saved in /tmp/testfile.pub. The key fingerprint is: 43:57:d1:18:24:6a:19:f4:cf:d0:49:d0:16:e0:89:4e langley@sophie The key's randomart image is: +--[ RSA 2048]----+ | .o +=B* | | B *+.. | | E *.o | | = . + | | S o | | . | | | | | | | +-----------------+
Installing your public key
The next step is to install the public key "id_rsa.pub" (not the private key, id_rsa) on the machine that you want to login in to; put it in the .ssh/ subdirectory as new file called authorized_keys. The sshd is generally very picky about permissions, so you may have to fiddle with them a bit.
Use ssh -v for debugging.
Other ssh tricks
- sshfs -- it lets you mount an arbitrary subdirectory locally. SUPER useful.
- ssh -D SOMEPORT -N -- enables port forwarding. This lets you create a quick, informal "VPN-lite". Very useful for accessing web applications from an internal ip number when you are on the outside of a network.
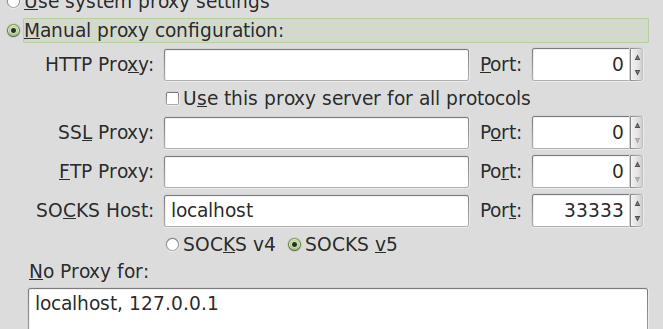
Setting your proxy in Firefox
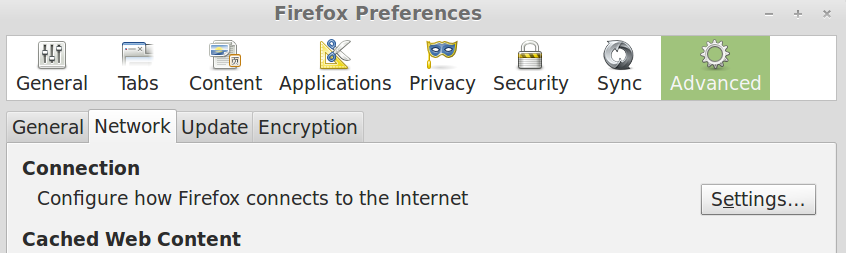
Setting your proxy in Firefox